Zatanna, a YC W26 company, just launched Kampala, a tool that sits between you and any app to capture exactly what's happening over the wire. The pitch is simple: point it at a website, mobile app, or desktop application, and it intercepts every HTTP/S request in real time. Then it converts those captured workflows into stable APIs you can actually use. For anyone who's spent hours reverse engineering some internal tool's undocumented API, this matters.
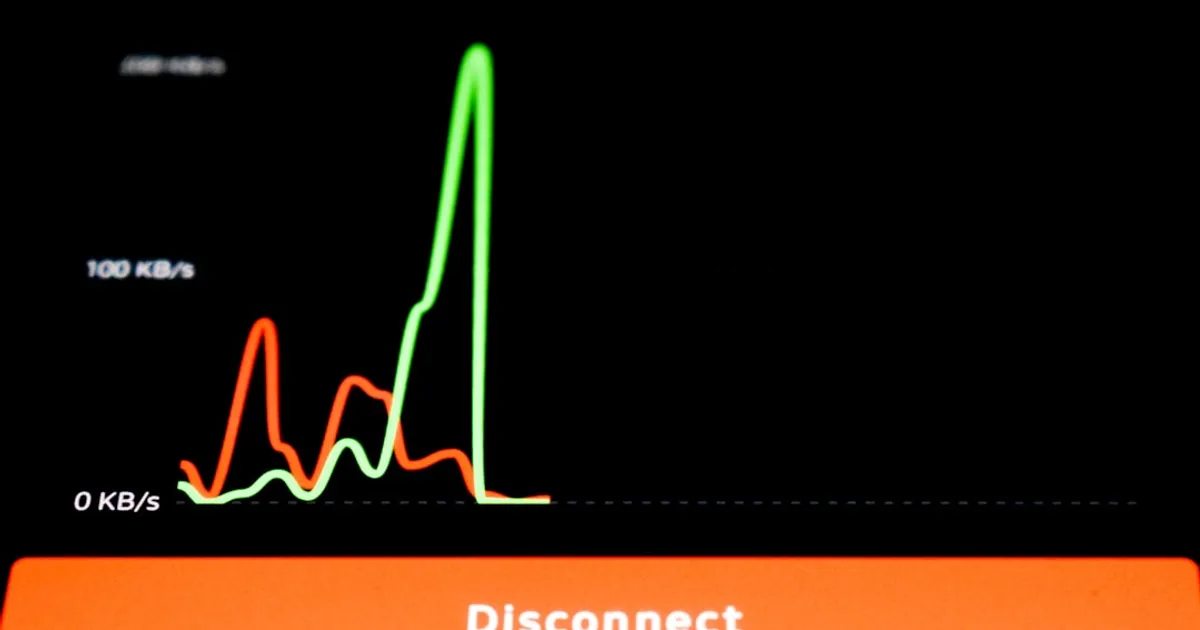
Capturing traffic is the easy part. Making it work reliably is where things get hard. Caido, a company building similar technology for vulnerability reproduction, pointed out in the Hacker News discussion that authentication chains are difficult to get right, and most users underestimate how tricky session management can be. TLS fingerprinting is another beast. No single TLS library covers all extensions, so tools like Kampala need to bundle multiple libraries to perfectly mimic the original client. Miss the fingerprint and servers reject your traffic outright.
Commenters on Hacker News shared their own workarounds for this problem. One developer described using ctx to analyze HAR files, generate OpenAPI specs, and build Python scripts implementing the Model Context Protocol. They used Playwright to handle authentication by launching a controlled browser, extracting credentials, and caching them locally. It worked, even in locked-down corporate environments. But that's a lot of glue code to maintain.
Kampala is macOS only for now, with a Windows waitlist. The real question is whether the tool can handle the messy auth flows that break everything else.